Okta: More than Usernames and Passwords
How a Company Shaped the Modern Identity and Access Management (IAM) Market
Thank you very much for reading and subscribing to my newsletter. I hope you'll find the SaaS Realm to be a valuable tool for your research or business. If you do, I'd appreciate it if you could share the newsletter with your friends and colleagues.
In addition, I am opening office hours for those interested to discuss further about SaaS. These are 30 minute slots I am opening each week to talk with my readers. Here is my calendly to schedule a chat.
This edition covers Okta, the leading independent provider of identity solutions for the enterprise. The company name might be familiar as they are used in multiple applications across the web with customers such as Openai and Zoom using their platform to sign-in their customers. To understand their products requires specific knowledge of the identity, authentication and authorization ecosystems. The Identity and Access Management industry has a lot of traits that are unique and, therefore, before diving into Okta we will focus on reviewing its core principles.
What is Identity and Access Management (IAM) ?
Identity and access management is a cybersecurity solution category that focuses on managing user identities and access permissions. The purpose of IAM is to ensure that the right users and devices can access the right resources and applications at the right time. This means, to keep hackers out while keeping their users in with the right permissions.
This has become complex as modern environments now function in on-premise, remote, and multi-cloud, which in turn have access to different devices, applications and third parties. IAM solves complexity by using the concept of a centralized identity, that assigns a single digital identity (sign-in) with access privileges for each user. That way, only authorized users can handle company resources and they can only use the resources the company permits.
To achieve this technological feat, several technological protocol advancements were needed to allow interoperability between computer networks access and permissions. This is because in the advent of the internet, identity use cases were built for one-dimensional authentications. Users imputed their logins and passwords into a designated form that checked for a match on a database to grant access. If there was a match, access was granted to the user. This workflow worked well only in simple HTTP and ethernet protocols.
As use cases rapidly became more complex by the early 2000s, new frameworks were needed to authenticate the identity of users that had to access multiple systems. As a result, the single sign-on (SSO) was then introduced in 2002 in the form of the Security Assertion Markup Language, or SAML. SAML was built on top of cookies and was effective at authenticating users in multiple systems.
Then in 2007, two major shifts occurred that required developers to rethink authentication. First, the smartphone was released with cookies that did not work as well as their desktop counterparts. Second, social companies such as Facebook had begun attempting to gain user authorization and permission to access users' contact lists in their emails. At that time, the process required users to share their email´s login and password so they could access their user's contact data. Companies literally accessed users' accounts to gather their contact list.
From any point of view, this was not a secure way to access users' contact data. A solution came from an open-source protocol, OAuth, released to create an authroization framework in which the email provider could share only the designated data. The protocol used a sign-on process that created an access token by the owner of the data such as google (gmail) to the one requesting that has permission (facebook) that provided access only to the specific data (contact list) from the consumer. This was the first instance of authorization where applications could gain authorization across the web within other instances.
On top of OAuth a new application was developed in 2014, OpenID Connect, an open source protocol that added 10% extra code for the developer and allowed the users to access their account with a different account login credential. In other words, OpenID enabled oAuth to not only have authorization capabilities but also authentication. This allowed applications such as sign-in with google or facebook into accounts in different applications as it provided a standardized way for a user to authenticate their identity with a different login credential.
With the existence of the standard protocols and the combination of applications of SAML, Oauth and OpenID Connect developers were able to provide enterprise and consumers with Single-Sign on Technologies (SSO). These applications then have been the backbone of the IAM markets allowing companies such as OKTA to exist. SSO and Multi-Factor Authentication (MFA) form the core of the IAM industry enabling authorization and security in the identity ecosystem.
Company Overview
Okta seeks to become the foundation for secure connections between people and technology by operating as a cloud-based identity solution. Okta allows their customers to integrate with nearly any application, service or cloud through a secure, reliable and scalable platform and cloud infrastructure. Their solution, the Okta Identity Cloud, allows their customers to secure their users with the applications they need by managing and securing all of their identities.
As organizations increasingly rely on complex technology stacks comprising multiple applications and systems, identity management has become critical for controlling permissions and access. Developers are tasked not only with ensuring system security but also with maintaining user accessibility. Given the technical expertise and resource allocation required for in-house solutions, many organizations opt for OKTA, benefiting from its scalability, interoperability, efficiency, and security.
Based on foundational protocols such as SAML, OAuth, and OpenID Connect, Okta operates as a cloud-based SaaS identity solution for organizations. Its core products—Workforce Identity and Customer Identity Clouds—are utilized by thousands of organizations and millions of individuals for secure access to a diverse range of technological assets, including cloud services, mobile applications, web platforms, SaaS products, on-premise solutions, APIs, and other IT infrastructures. Employing a SaaS business model, Okta generates revenue through subscription-based cloud offerings.
Company History
Founded in 2009 by Todd McKinnon and Fredrick Kerrest, both former Salesforce executives, Okta was established at the height of the financial crisis. McKinnon and Kerrest recognized a crucible moment: applications were increasingly migrating to the cloud, necessitating more advanced identity protocols. They secured their first institutional funding through a modest $750,000 seed round from angel investors—a small sum compared to today's investment landscape. Following some initial traction, Andreessen Horowitz (A16Z) led their Series A funding, followed by participation from Sequoia, Khosla, and Greylock in subsequent rounds. Before going public, the company completed private fundraising up to a Series F round.
Eight years after its inception, Okta filed for its IPO in March 2017 and raised $187 million in the initial public offering. At that time, the largest stakeholders were Sequoia, A16Z, and Greylock, each holding more than a 15% ownership stake. Since then the company has raised $1 billion in post-IPO equity and acquired Auth0 for $6.5 billion which increased use cases from enterprise identity to customer identity and access management (CIAM).
Product
Okta is an cloud-based identity solution designed as one platform, the okta identity platform, with two distinct use cases. The product is designed to serve enterprise grade identity needs with the flexibility and customization to work in over 7000 integrations across the cloud, mobile, web applications and IT infrastructure providers.
Workforce Identity Cloud
The first, the Workforce identity Cloud is used by organizations to manage and secure their employees, contractors and partners. The solution works on an identity-centric approach becoming the central system for an organization's connectivity, access, authentication and identity lifecycle management needs for all their users, technology and applications. The workforce Identity platform enables workforces to have immediate and secure access to every application from any device they use by enabling administrators to enforce contextual access management decisions based on the user identity, device, location, IP and time of day. This is done without requiring multiple credentials significantly enhancing their users' connectivity and productivity. In addition, the Workforce identity platform has several additional offerings for their customers as:
Adaptive Multi-Factor: Authentication which acts as an additional security layer for managing access and permissions
Universal Directories: Okta solution to act as a system of record for the customers to organize and manage their users.
Lifecycle Management: that enables customers to manage users' access privileges through their entire lifecycle with a no-code approach that improves administrative efficiency and productivity.
Okta Identity Governance: an unified identity access management and identity governance solution that enables customers to improve security and compliance reducing security risk while increasing efficiency
Advanced Server Access: a product designed to secure on-premise and cloud-based access to servers.
Access Gateway: application to extend services from workforce identity cloud to their existing on-premises applications
Customer Identity Cloud
The second use case vertical, Customer Identity Cloud, specializes in enabling, managing, and securing the identities of client users through APIs. This product functions as a Customer Identity and Access Management (CIAM) solution and is built atop Auth0's developer focused tools. It empowers organizations to improve customer experiences by simplifying the complexity of identity management. Using the Customer Identity Cloud, developers can easily create customer-facing identity applications for cloud, mobile, and web platforms, using the solution's extensible and customizable features.
The Customer Identity Cloud is designed to be easily integrated into their customers' existing cloud, web, and mobile environments through comprehensive APIs, Software Development Kits (SDKs), and a wealth of developer community resources. This ease of integration facilitates rapid value realization. With the customer identity cloud organizations that prioritize user experience and security in identity management often witness heightened levels of customer acquisition, retention, and loyalty. In addition, the Customer identity platform has several additional offerings for their customers as:
Universal Login: Universal Login is a standards-based login infrastructure with centralized feature management and configuration for websites and applications that can be integrated with a wide range of social providers, enterprise login services and customer-provided databases.
Attack Protection: Attack Protection is a suite of security capabilities that protect their customers from different types of malicious traffic, including bots, breached passwords, suspicious IP addresses and brute force attacks
Passwordless Passwordless authentication enables users to login without a password and supports a variety of different login methods, including advanced device biometrics.
Machine to Machine: Machine to Machine provides standards-based authentication and authorization with non-interactive devices and applications.
Private Cloud: Private Cloud is a deployment option that allows their customers to run a dedicated cloud instance of the Customer Identity Cloud. Private Cloud capability supports multiple cloud providers.
Organizations: Organizations enable their customers to support a large number of partners or customers of their own with independent configurations, login experiences and security options.
Actions and Extensibility: Actions and Extensibility allows their customers to visually drag and drop Actions to build custom identity flows that address their unique requirements.
Enterprise Connections: Enterprise Connections enable Enterprise Federation using pre-built integrations with commonly used Enterprise Identity Systems.
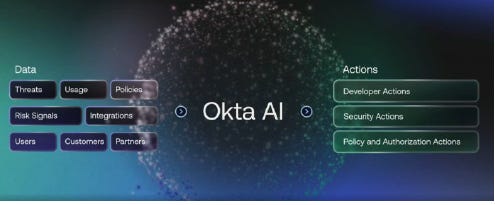
Moving forward the company has announced innovations that included both Workforce Identity products like Identity Threat Protection , Universal Logout, and Log Investigator, as well as Customer Identity products like Passkeysand Fine-Grained Authorization . In addition, Okta AI was released.
Business Model
Okta operates on a SaaS business model generating revenue primarily from multi-year subscriptions to its cloud-based offerings. The company invoices customers in advance on an annual basis, with subscription services accounting for 97% of its total revenue. Their customer growth strategy focuses on a "land and expand" model, where initial acquisition is followed by upselling additional features or expanding the number of users.
Capitalizing on their reputation for secure solutions, Okta collaborates with industry giants like Amazon Web Services (AWS), CrowdStrike, Google, LexisNexis Risk Solutions, Microsoft, Netskope, Palo Alto Networks, Plaid, Proofpoint, Salesforce, ServiceNow, VMware, Workday, Yubico, and Zscaler. The company operates on a flywheel model; as they add new customers, users, developers, and integrations, the value and security of their Workforce Identity and Customer Identity Clouds simultaneously increase for all stakeholders. The network effects increase the depth and breadth of their offerings, evidenced by over 7,000 integrations as of 2023.
By the end of the first half of 2023, Okta's customer base has grown to 18,400 organizations. Their customers vary from leading global enterprises to small- and medium-sized businesses, as well as educational institutions, nonprofits, and government agencies.
Total Addressable market
The company estimates an $80 Billion addressable market for their applications in Workforce Identity and Identity Governance and Administration (IGA). This calculation is based on an estimation of 50,000 U.S. businesses with more than 250 employees (per 2019 U.S. Bureau of Labor Statistics) multiplied by 12-month ARR assuming adoption of all their current products and announced IGA products which implies a market of $21 billion domestically, then multiplied by two to account for international opportunity.
As for Privileged Access Management (PAM), its $30B TAM based on internal estimates of Modern Infrastructure Access spend as a percent of Total Cloud Spend based on Gartner Forecast Analysis: Public Cloud Services, Worldwide report. $30B
And the remaining, Customer Identity, TAM is based on 4.4 billion combined Facebook users and service employees worldwide multiplied by internal application usage and pricing assumptions.
Go-To-Market
Okta employs a two sided go-to-market strategy, engaging customers both directly, through inside and field sales, and indirectly via a broad network of channel partners.
The direct salesforce is structured to address specific needs of each segment of their target markets. This leads to a division based on geography, customer size, and industry vertical. Navigating the technicalities of sales, the team has support of sales engineers, security teams, cloud architects, and professional services to effectively usher leads down the sales funnel.
Concurrently, indirect sales uses Okta's partner ecosystem to increase sales. They do this by not only integrating Okta's solutions into their products but also through strategic selling arrangements. Additional channel partners such as system integrators and traditional value-added resellers expand the customer reach even further.
To support this go-to-market strategy, Okta has established a strong, data-driven, marketing practice. They focus on increasing awareness and reputation of Okta as the industry-leading identity platform, cultivating a robust brand presence to generate leads and engage the community. A cornerstone of this effort is their annual customer conference, Oktane, where customer success stories, new product launches, and organizational announcements take center stage.
The efficacy of this standard strategy has proven to be highly effient, as Okta stands as an independent leader in Identity and Access Management (IAM), as depicted in the exhibit below.
Financials
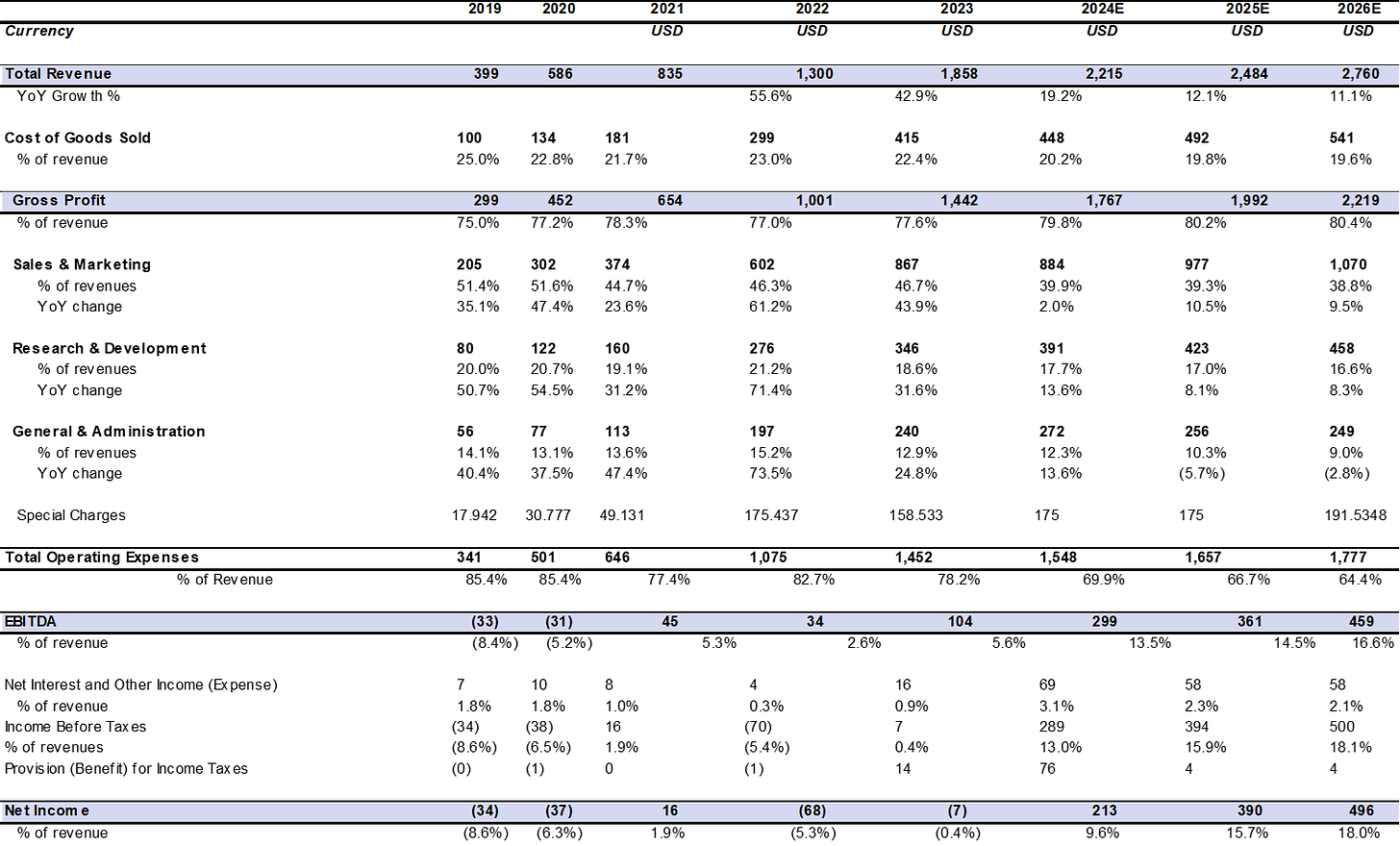
Okta has been on a shift into profitability after their acquisition of Auth0 and the shift from market dynamics from growth to capital efficiency. The pace of change has been slower than other industry counterparts as the company is taking longer to achieve GaaP operating Income, however, the company continues to have strong growth of 23% YoY. Here are the financial highlights:
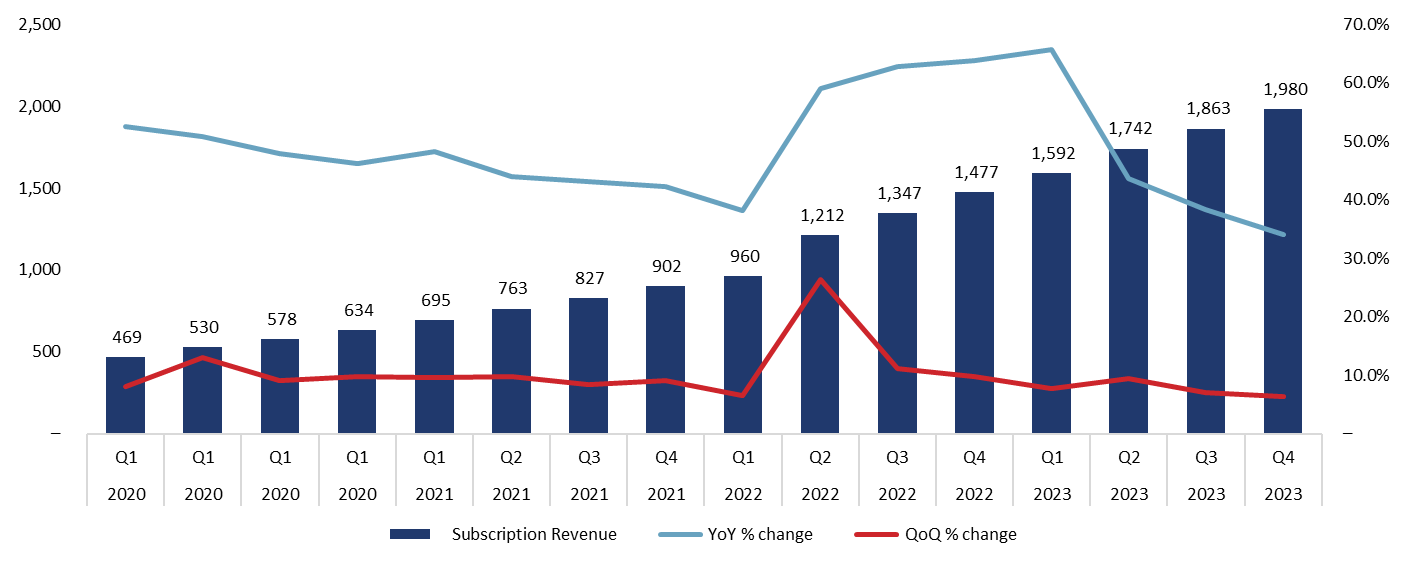
Revenue: Total revenue was $556 million, an increase of 23% year-over-year. Subscription revenue was $542 million, an increase of 24% year-over-year.
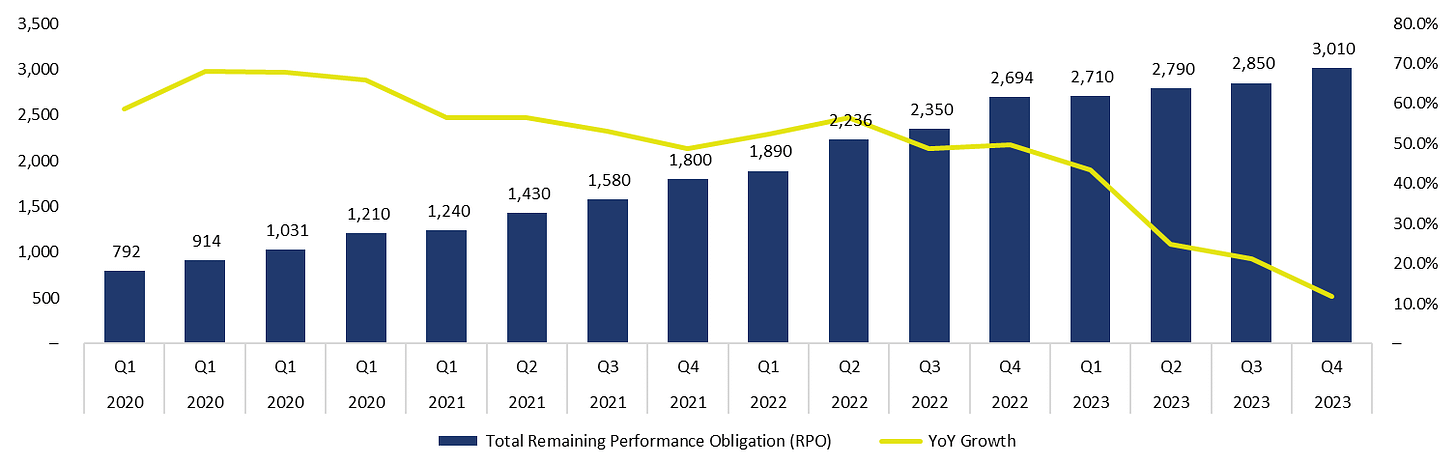
RPO: RPO, or subscription backlog, was $3.03 billion, an increase of 8% year-over-year. cRPO, which is the subscription backlog expected to be recognized over the next 12 months, was $1.77 billion, up 18% compared to the second quarter of fiscal 2023.
GAAP Operating Loss: GAAP operating loss was $162 million, or (29)% of total revenue, compared to a GAAP operating loss of $208 million, or (46)% of total revenue, in the second quarter of fiscal 2023.
Non-GAAP Operating Income/Loss: Non-GAAP operating income was $59 million, or 11% of total revenue, compared to a non-GAAP operating loss of $15 million, or (3)% of total revenue, in the second quarter of fiscal 2023.
Cash Flow: Net cash provided by operations was $53 million, or 10% of total revenue, compared to net cash used in operations of $19 million, or (4)% of total revenue, in the second quarter of fiscal 2023. Free cash flow was $49 million, or 9% of total revenue, compared to negative $24 million, or (5)% of total revenue, in the second quarter of fiscal 2023.
Cash, cash equivalents, and short-term investments were $2.11 billion at July 31, 2023. During the quarter, the company repurchased $142 million principal amount of the convertible senior notes due in 2025, and $242 million principal amount of the convertible senior notes due in 2026, resulting in a gain on early extinguishment of debt of $42 million.
For the full year fiscal 2024, the Company forecasts:
Total revenue of $558 million to $560 million, representing a growth rate of 16% year-over-year;
Current RPO of $1.780 billion to $1.785 billion, representing a growth rate of 13% year-over-year;
Income Statement ($M)
ARR ($M)
Remaining Performance Obligation ($M)
The remaining Performance Obligation is contracted revenues that customers are contractually bound to spend in the future.